Sophos Maze Ransomware
The gang responsible for the Maze ransomware family conducted an attack in which they distributed their malware payload inside of a virtual machine (VM).
Sophos Maze Ransomware
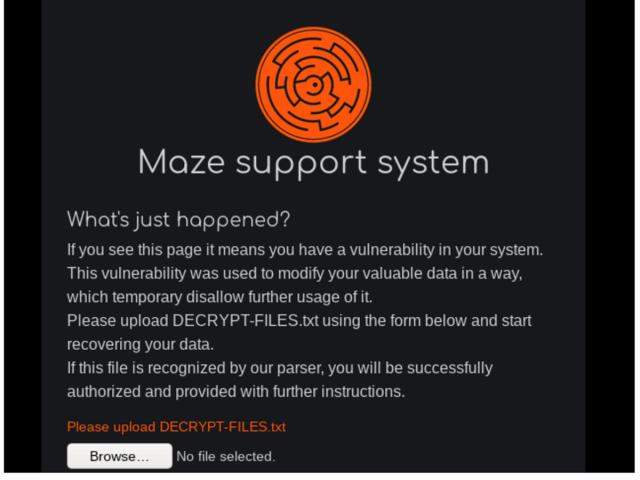
Normally, the answer would be technical or organisational, but a new type of ransomware called Maze seems to have stirred up a very different response in one of its recent victims – bring in the lawyers and try to sue the gang behind it. Sophos, the global provider of next-generation cybersecurity solutions, has published a report, “Maze Attackers Adopt Ragnar Locker Virtual Machine Technique,” which shows how attackers tried three. Another ransomware trend is “secondary extortion,” where alongside the data encryption the attackers steal and threaten to publish sensitive or confidential information, if their demands are not met. In 2020, Sophos reported on Maze, RagnarLocker, Netwalker, REvil, and others using this approach. May 12, 2020 As SophosLabs explains in the new report, the Maze crew was one of the first ransomware gangs out there to turn to a combination of blackmail and extortion, demanding that victims pay what is effectively hush money as well as a kidnap ransom. Ransomware operators are always on the lookout for a way to take their ransomware to the next level. That’s particularly true of the gang behind LockBit. Following the lead of the Maze and REvil ransomware crime rings, LockBit’s operators are now threatening to leak the data of their victims in order to extort payment.
Sophos’ Managed Threat Response (MTR) observed the technique in action while investigating an attack that occurred back in July 2020.
In that incident, the attackers packaged the ransomware payload inside of a Windows .msi installer file that was more than 700MB in size and distributed it onto the VM’s virtual hard drive.
An investigation into the attack revealed that the malicious actors had been present on the targeted organization’s network for at least six days prior to distributing their ransomware payload. During that period, they had built lists of internal IP addresses, used one of the organization’s domain controller servers and exfiltrated information to their data leaks site.
This dwell time could explain the existence of certain configurations of the Maze-delivered VM. As quoted by Sophos’ MTR in its research:
The virtual machine was, apparently, configured in advance by someone who knew something about the victim’s network, because its configuration file (“micro.xml”) maps two drive letters that are used as shared network drives in this particular organization, presumably so it can encrypt the files on those shares as well as on the local machine. It also creates a folder in C:SDRSMLINK and shares this folder with the rest of the network.
Sophos Maze Ransomware Attack
The campaign described above wasn’t the first instance in which attackers have delivered ransomware inside a virtual machine. Back in May 2020, Sophos’ MTR spotted the Ragnar Locker crypto-malware family pull the same trick.
The virtual machine in that attack ran Windows XP as opposed to the Windows 7 instance on the VM containing Maze. Furthermore, the latter VM was larger in size in order to support additional functionality.
Sophos Maze Ransomware Free
This technique highlights the need for organizations to defend themselves against a ransomware infection. They can do so by working to prevent a crypto-malware attack in the first place.